Because the best brands — and the best industries — remember who built the foundation.
March is Women’s History Month, which means social media is currently experiencing its annual surge of: “Celebrating the incredible women in our organization!”
And while that’s nice…it also slightly misses the point.
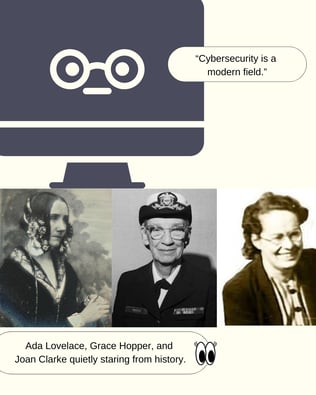
Cybersecurity didn’t suddenly discover women in 2026.
Women helped invent the field before we even called it cybersecurity. 🎤
The OG Cyber Architects
Before we had threat intelligence feeds, zero-trust frameworks, and vendors promising to “solve cyber with AI,” there were a few people quietly solving the actual problem: making computers work securely.
Among them:
Ada Lovelace 👉 often called the 1st
computer programmer

In the 1840s, she wrote what is widely considered the first computer algorithm.
Yes… You read that right...1840s.
Before computers existed.
If cybersecurity is about protecting digital systems, Lovelace helped invent the logic that made those systems possible.
Not a bad start.
Grace Hopper 👉 Computer Scientist &
U.S. Navy Rear Admiral
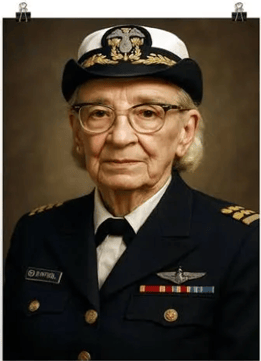
Grace Hopper didn’t just write code. She made it human-readable.
Her work on compilers and COBOL turned computing from something only mathematicians could understand into something organizations could actually use.
Which means every modern security tool, cloud platform, and AI model exists partly because Hopper made software scalable.
Also: she literally coined the term “debugging.”
Joan Clarke 👉 English cryptanalyst who worked as a code-breaker in WWII

At Bletchley Park during WWII, Joan Clarke worked alongside Alan Turing, helping crack the Enigma encryption system.
Translation for modern cyber folks:
She helped break one of the most sophisticated cryptographic systems of the time.
Cryptography → encryption → cybersecurity.
Same lineage.
Which brings me to this point: Lineage matters because it reminds us that today’s “new” ideas rarely start from scratch.
Cybersecurity Is Actually a Lineage
The industry loves to talk about innovation. But cybersecurity isn’t really a “new” field.
It’s an evolution of mathematics, cryptography, computing, and engineering built by generations of thinkers.
And many of them were women.
From early programming pioneers to cryptographers to today’s leaders shaping cyber policy, threat intelligence, and AI security.
The Branding Lesson (Because This Is Still the Brand Wagon)
Here’s where the marketer in me kicks in.
Industries — just like brands — tell stories about themselves. Sometimes those stories get simplified. Sometimes they get rewritten.
And sometimes the real origin story gets buried under buzzwords like:
-
AI-driven security
-
Next-gen cyber defense
-
Autonomous SOCs
-
Quantum-resistant encryption
But the strongest brands don’t erase their history. They build on it.
Why This Matters Right Now
Cybersecurity is entering another turning point.
AI systems are being deployed everywhere.
Boards are asking new questions about digital risk.
And security leaders are redefining what “defense” even means.
👉 Every major shift in computing — from early programming to cryptography to cloud to AI — was built on the work of people who thought differently about technology.
A Thought for Women’s History Month
Instead of only celebrating women currently in cybersecurity…maybe the better tribute is recognizing that they’ve been shaping it all along.
Not as a trend.
Not as a diversity initiative.
But as architects of the systems we now spend our careers protecting.
Final Thought (Because It’s Sunday)
Cybersecurity didn’t start with a SIEM dashboard.
It started with mathematics, code, and cryptography.
And a surprising number of the people behind those breakthroughs were women.
And if your brand story conveniently forgets who built the foundation…
you might want to check whether your narrative is secure. 😉
.jpg?width=600&height=300&name=TLS%20BW%20Website%20Logo%20(2%20x%201%20in).jpg)
-2.jpg?width=600&height=300&name=TLS%20BW%20Website%20Logo%20(2%20x%201%20in)-2.jpg)